Stay Grounded
Building Cyber Resilience: A Roadmap for Healthcare Security and Compliance
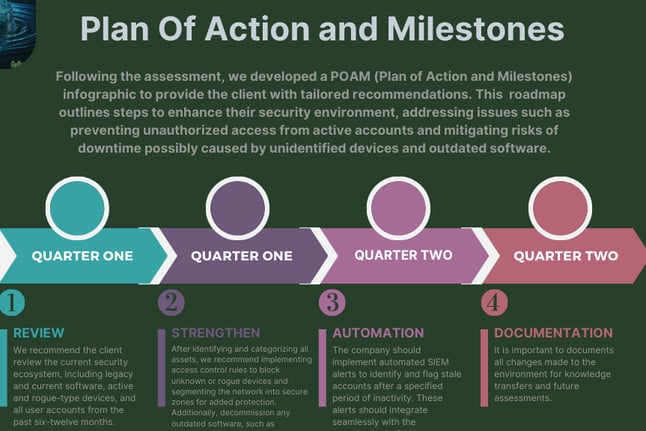
This project aims to enhance cyber resilience in healthcare organizations by ensuring compliance with HIPAA and strengthening defenses against cyber threats using the CIS Controls framework.
Case Study: HealthCare
Context:
Performed a CIS Assessment and mapped controls to HIPAA to identify gaps.
Size: 100 employees, 5 years in operation
Current Problem:
unidentified devices and outdated software which the organization is due to recurring downtime.
Active accounts for former employees created security risks.
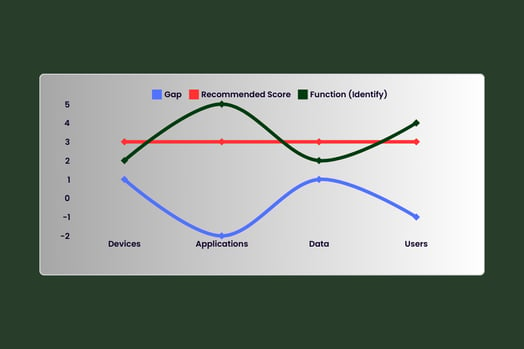
The gap highlighted in blue represents the gap, revealing deficiencies in device visibility, application management, data protection, and user account management. The recommended score (in red) reflects where the organization needs to be to ensure compliance with HIPAA and strengthen cyber resilience. The green line correlates to the identify function, showing the total score of each control and its safeguard (sub-control), correlating to each asset shown at the x-axis. Based on our assessment, the organization is progressing toward a secure environment, achieving a recommended score of 3. However, gaps in device management and user account controls suggest opportunities to strengthen existing processes and enhance overall security posture.
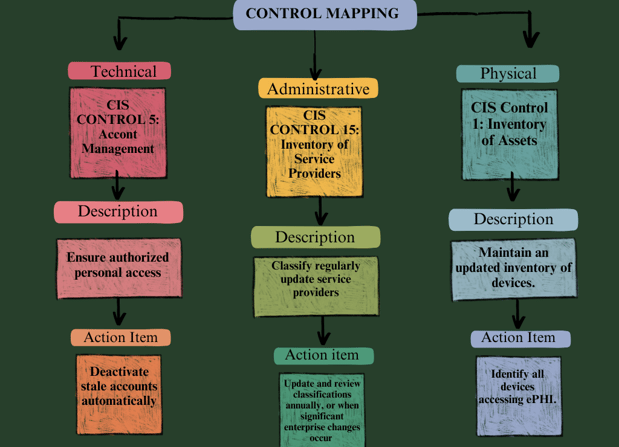
Mapping CIS Controls To HIPAA
In our recent client engagement, the main task was to ensure the healthcare organization met certain HIPAA requirements. Mapping CIS Controls to HIPAA ensures that healthcare organizations can strengthen their cybersecurity posture while maintaining compliance with regulatory requirements. This alignment provides actionable safeguards to protect sensitive patient data. Here is a highlight of key requirements we correlated , along with recommended action items to ensure compliance :
Administrative Safeguards: Policies and procedures to manage and protect ePHI.
Physical Safeguards: Measures to protect physical access to systems storing ePHI.
Technical Safeguards: Technologies to secure ePHI against unauthorized access.